The Risks of Data Tampering and How to Prevent It - Ocala, Gainesville, Orlando | Verteks Consulting, Inc.

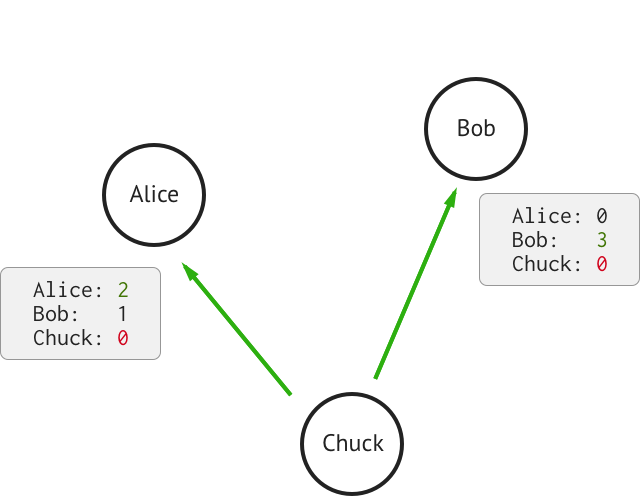
Database Tampering and Detection of Data Fraud by Using the Forensic Scrutiny Technique | Semantic Scholar

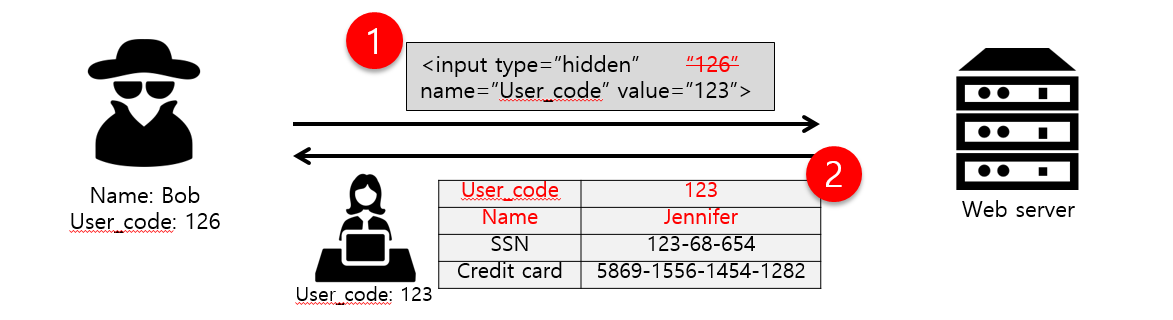
Parameter tampering cyberattack and event-trigger detection in game-based interactive demand response - ScienceDirect
Two fingers are decorated as two person. They are discussing about data tampering Stock Photo - Alamy